Certificate Transparency: What Do Domain Owners Need To Know?

Google has recently been at the forefront of sweeping industry changes to improve the security behind SSL issuance. The next round of changes impacting certificate holders is about to go live, and it’s important for domain owners to take notice.
More…
From April 30, 2018, Google Chrome will consider SSL certificates that aren’t included in a Certificate Transparency log to be insecure. When Google Chrome users visit a site secured by an unlogged SSL certificate issued after that date, they will see a prominent warning indicating that the site is insecure.
Continue reading to find out how Certificate Transparency may impact your business, and what to do to stay protected.
Certificate Transparency is a Google-backed scheme intended to close a gap in the public key infrastructure used to verify the identity of hosts and to encrypt network connections. Without Certificate Transparency, online security and privacy depend on the trustworthiness of Certificate Authorities, which are capable of issuing browser-trusted certificates for any domain.
In the last few years, incidents in which Certificate Authorities have issued certificates without the permission of domain owners have underscored the limitations of the current system. Certificate Transparency requires that all certificates are recorded in publicly accessible logs when they are issued. Because the logs are publicly accessible, domain owners can see any certificate that has been issued for their domain.
Google has considered extended validation certificates without Certificate Transparency to be insecure since 2015. From April 2018, that judgement will be extended to all unlogged certificates, including Domain Validated and Organization Validated SSL certificates.
Before we look closer at the Certificate Transparency framework and its motivation, it is important that domain owners and hosting clients understand the following:
- Google Chrome will only require that certificates are logged if they were issued after April 30, 2018. Certificates issued before April 2018 will still be trusted.
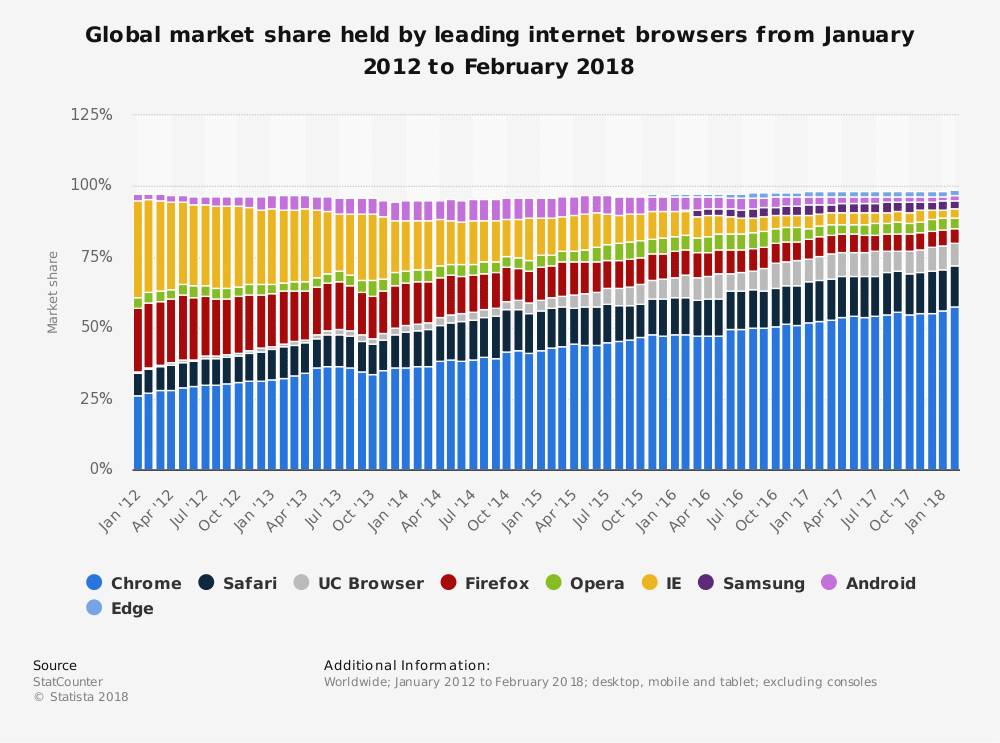
- Google Chrome’s market share stands at almost 60%. Using certificates issued by a CA that doesn’t support Certificate Transparency will have a massive impact on user trust.
- For the most part, domain owners will not have to do anything other than choose a Certificate Authority, such as Comodo, that supports Certificate Transparency.
- Certificate Transparency makes the web safer for users and domain owners.
The Problem With Certificate Authorities

SSL certificates are an essential component of online security and privacy. They are used to encrypt connections between browsers and hosts, and, just as important, they are used to verify that the host is authorized to serve content from a domain. Without that verification, it is impossible to be certain that a client is connected to the expected domain and not to a malicious host that can read and modify data traveling over the connection.
For SSL certificates to be useful, the identity of the applicant must be verified before a certificate is issued. That is the role of Certificate Authorities. CAs verify the identity of the applicant and that they have legitimate control over a domain: domain validation, organization validation, and extended validation involve increasing levels of scrutiny and stringency.
After validation, Certificate Authorities sign SSL certificates with their root certificate. Browsers trust a limited number of root certificates absolutely. If an SSL certificate is signed by a trusted root certificate, it is trusted by browsers.
Certificate Authorities are the weak link in the chain. If a CA is hacked, subverted, or incompetently managed, it may issue and sign certificates without the permission of a domain’s legitimate owner.
In 2011, Dutch Certificate Authority Diginotar was hacked and illegitimately issued signed certificates for many domains, including Google-owned domains. WoSign and its subsidiary StartCom issued unauthorized certificates for various domains; their root certificates were removed from browsers, causing disruption for their customers. Symantec issued thousands of certificates without the permission of domain owners.
Certificate Transparency provides added accountability for Certificate Authorities and a mechanism for domain owners and browser developers to check whether certificates have been issued without proper authorization.
What Is Certificate Transparency?

Certificate logs are at the heart of Certificate Transparency. Each log is a network service that contains a publicly accessible list of SSL certificates. The logs are append-only — certificates can be added, but not removed — and use advanced cryptographic techniques to guarantee they haven’t been tampered with.
Under Certificate Transparency, Certificate Authorities are required to add every certificate they issue to one or more logs. Domain owners and other interested parties can check the logs to see if certificates have been issued without permission.
The logs are only effective if Certificate Authorities are required to add all the certificates they issue. To motivate Certificate Authorities and protect its users, Google Chrome will no longer trust any certificate that has not been added to a certificate log, even if it has been signed by a CA’s trusted root certificate.
Before Certificate Authorities issue an SSL certificate, they can submit a pre-certificate with the relevant details to a certificate log, which will respond with a Signed Certificate Timestamp (SCT), proof that the certificate has been logged. The SCT should be included in the SSL certificate when it is issued so that browsers can verify that it has been logged. This is the most common way to prove that a certificate has been logged, but there are other techniques, including a TLS extension and OCSP stapling, both of which require a special server configuration, whereas adding the SCT to the certificate “just works”.
The Certificate Transparency framework includes other components, such as monitors that watch certificate logs for suspicious certificates, and auditors, which are software components that can be included in browsers and other software to verify that logs are behaving correctly and that a specific certificate is included in a log.
Benefits of Certificate Transparency

Certificate Transparency addresses a serious problem with the Certificate Authority system, enhancing security and privacy for domain owners and their users and customers.
- Certificate Logs make it easy for domain owners to discover if a certificate has been issued for their domain by any Certificate Authority.
- If an SSL certificate is issued without permission by a CA, it won’t be trusted by Google Chrome (and other browsers in the near future).
- When a Certificate Authority “goes rogue” it will be easier to find and mitigate the problem, limiting risk and disruption.
- The SSL certificate system isn’t entirely dependent on the trustworthiness of every CA with a trusted root certificate.
In short, Certificate Transparency will make domain owners, server hosting clients, and web users safer.
What should I do to stay protected?
Domain owners should choose a Certificate Authority that supports Certificate Transparency to ensure that visitors to the site using Google Chrome are not presented with a warning message.
We recommend purchasing certificates from Comodo as they fully support Certificate Transparency and have been a trusted Certificate Authority for years.
Looking for more ways to keep your server secure? Contact us today to discuss our extensive server management and security solutions.
Was this page helpful?

